What is Information Technology (IT)?
Greetings & Salutations!
When I decided to go into Cybersecurity, it wasn’t just on some random whim. I love helping people fix their computer issues, whether it be hardware or software. I love breaking the jargon into an understandable format for non-tech-savvy individuals. I love the thought of protecting a company in the same way as how I would want to protect my family in the digital world. Cybersecurity is just a tiny area of the all-encompassing title of Information Technology. Today, I want to review the different areas within this branch of Computer Science. So strap in my Fellow Weirdos with Awkward Seasoning; we’re about to go for a joy ride!
What is Information Technology (IT)?
My definition of Information Technology (IT) is the field of accessing information via computer systems or devices that have access to the Internet. Breaking this down a little more would be that IT is the hardware and software used to create, communicate, display, manipulate, store, and transmit data.
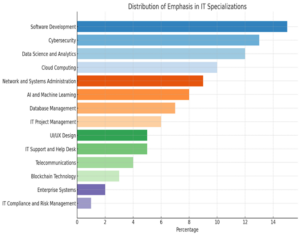
IT Specialization Breakdowns
Within IT, particular specializations cater to the different aspects of technology and business needs. The bar graph below shows the relative importance of each specialization in the current IT landscape. This does not say that one specialization is better than another; it only refers to the business needs listed in our current data.
Software Development is the process of creating, designing, testing, and maintaining software applications. A software application is a user interface that performs a specific task or set of functions. For example, you can access your email account and read messages. A software development team designed the access to your email account and then turned it into a software application for your convenience. Gmail, Yahoo, and Outlook are examples of these types of applications.
Cybersecurity uses specialized technologies to shield systems, networks, programs, and devices from unauthorized access and harmful intentions. Imagine playing a strategy video game where you must protect your base. You build a wall around your base that only your allies can enter or exit using a unique access code. The wall is a protective barrier, and you’ve authorized your allies to bypass it. The wall acts as a deterrent to enemy players. While enemies might still try to access the wall, its existence significantly lowers the likelihood of a successful invasion.
Data Science & Analytics involve collecting, processing, and analyzing large datasets using various calculations and computational methods to uncover meaningful insights and provide knowledgeable data. You can compare Data Science and Analytics to your Spotify Yearly Wrap. It gathers all the songs and artists you’ve listened to over the past year, then reviews your choices to determine patterns in your listening habits. Then, it creates highlights of your favorite genres, songs, and artists in a pleasing-to-the-eye format with information it has determined you would enjoy learning about.
Cloud Computing focuses on delivering on-demand hosting services over the Internet, such as software, analytics, storage, servers, and databases. The cloud just refers to servers that are accessible via the Internet. Nvidia is a company that created the Nvidia GeForce Experience, which allows you to stream any game you have purchased from them directly from their cloud environment. It handles all the heavy strain it would put on typical hardware. So, instead of upgrading your computer to run a game smoothly, your computer would need the minimum specifications to access the Nvidia GeForce Experience.
Network & System Administration deals with the day-to-day maintenance, configuration, and reliable operation of an organization’s network and connected systems. It is the same as researching and implementing the best way to provide a reliable wireless connection throughout your home using the correct software and hardware.
As a Side Note, playing with the settings on my router makes me feel like a kid in a candy store.
Artificial Intelligence (AI) & Machine Learning are relatively new concepts in recent years. They encompass the creation of algorithms that can perform human-like tasks and learn from data without being told to do so. Take Netflix, for example. It uses your previous screen time and preferred genres to suggest new movies or products you might like. Systems like Alexa, Siri, or Google Assistant are called Smart devices and can understand your questions, provide answers, or set reminders with an auditory request.
Database Management is the process of organizing, designing, maintaining, and securing data storage systems to ensure performance, security, and integrity of data. If you’ve ever been to a hospital, you know that they keep patient information, medical records, and appointment schedules. The system that all this information is housed in is called a database, and the management of this system is to keep all this data secured so that it is quickly accessible by medically authorized staff. The people who work in the hospital need to keep the data safe to uphold the integrity of the information.
IT Project Management focuses on planning, organizing, executing, and overseeing projects, ensuring on-time and on-budget delivery of specific IT services and infrastructure. An IT Project Manager’s role would be similar to that of a wedding planner. Organizing a wedding requires meticulous planning, budgeting, and coordinating many moving parts. They have the highest priority of making sure everything runs smoothly to accomplish the goal at hand. IT Project Management requires the same meticulous efficiency to ensure the project is completed on time.
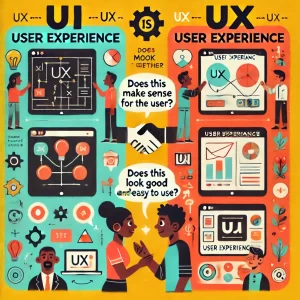
UI/UX Design involves creating a functional user experience by designing and improving the user interface of software applications. This is making digital interfaces more accessible and user-friendly. Most of the technological skills I have developed were through online learning platforms like Coursera, Udemy, and Khan Academy. Using the course dashboard will allow you to filter the course by duration, subject matter, and difficulty level. The way the course dashboard was created makes it easier for the user by adding items like tracking your progress, accessing course materials, and allowing submission of assignments without confusion.
IT Support & Help Desks are centralized areas that support long-term technological aspects and are crucial for maintaining an organization’s IT health. They are often the first point of contact for users experiencing infrastructure improvements and strategic planning issues. They are also the first line of defense when there is an outage at the company. When calls start pouring in, it can become overwhelming. However, working for the help desk in the past helped me develop time management, troubleshooting, patience, and prioritization skills, which are transferrable skills across careers. We will talk more about transferable skills in future posts.
Telecommunications or Telecom enables and manages the exchange of information over long distances via telephone lines, satellites, and the Internet. When you use your phone at your desk to make a call to another department, you’re using telecommunications technology. Your voice is converted into digital signals that travel over telephone lines or through ethernet networks, instantly allowing you to communicate across long or short distances.
Blockchain Technology is a decentralized database for data storage to increase the security and efficiency of cryptocurrencies, supply chain tracking, smart contracts, and healthcare clinical trials. When you make a purchase with Bitcoin, each transaction is recorded in a block and added to the chain of previous transactions. The record-keeping for these transactions is decentralized so they can remain transparent and nearly impossible to with, which provides a secure way to use digital money.
Enterprise Systems(ES) are the integration of an organization’s necessary applications, databases, software, hardware, and modules to support, maintain, and facilitate operations and processes. Customer Relationship Management (CRM) maintains interactions with current and potential customers. CRM systems have integrated data from sales, customer service, and marketing, which can be used to create a comprehensive view of each customer. Salesforce, HubSpot CRM, and Microsoft Dynamics 365 are enterprise systems.
IT Compliance & Risk Management helps maintain laws and regulations using IT standards and guidelines to ensure the company stays compliant and can manage risks effectively. If you are reading this, I guess you have heard of a compliance regulation called HIPAA. President Bill Clinton signed the Health Insurance Portability and Accountability Act (HIPAA) into law in 1996. It involves securing patient records through controlled access and regular audits of data usage and logs. Other regulations include Sarbanes–Oxley(SOC), ISO 270001, and NIST.
Now you have a breakdown of the different specialties in Information Technology. Even though I presented these as individual specializations, all these specializations can overlap. Cybersecurity is about defense and mitigation. However, most guidelines in Cybersecurity need to follow IT Compliance and Risk Management to protect organizations and their stakeholders. IT Support and Help Desks use and troubleshoot Enterprise Systems like Salesforce and Microsoft Dynamics 365. Software Development and UI/UX Design go hand in hand because their departments within an organization can maintain cross-functionality. This information I have provided gives you a better understanding of the Information Technology subsections. My next entry will go over the 1st rule of certifications, and then I’ll break down transferable skills using my experience to show you how to determine where your interests could lead you in Information Technology.
Thank you for joining me on this awkward ride through the basics of Technomacy.
I look forward to you reading next time!

